Problem – no WiFi after Fresh Install

After an upgrade from Mint 13 to Mint 16 using the “fresh upgrade” method again resulted in a system without wireless connectivity, this guide was created for future reference and possibly as an aid to others experiencing the same problem. The information here applies to the B43 driver, specifically for the 4311 PCI-ID/Chip ID, but the driver/firmware solution described may be similar for other Broadcom PC-IDs also using the B43 driver (see list below) and running on Debian/Ubuntu or derivative distros; however, keep in mind that derivative doesn’t imply compatibility in all cases. For further information about B43/B43 legacy wireless devices and driver/firmware solutions see https://wireless.kernel.org/en/users/Drivers/b43.
Similar PC-IDs for B43:
14e4:4307
14e4:4311
14e4:4312
14e4:4318
14e4:4319
14e4:4320
14e4:4357
14e4:5354
Note that in most cases PCI-ID correlates to the Chip ID, but that is not always the case, so identify your device using the PCI-ID.
Regardless of the PCI-ID, always check the distro’s documentation and user forums for the most up-to-date information. Broadcom wireless solutions change constantly and often vary from distro to distro.
System used for this Guide
The system used for this guide was an Intel Pentium T2310 / 1.46 GHz ( Dual-Core ) laptop with Mint 16 (Mate) freshly installed to the hard drive. The built-in wireless device was based on the BCM 4311 chipset. No other options existed at the time for connecting to the Internet except for wireless, which wouldn’t work after the OS installation.
Broadcom Wireless Issues
In the past, wireless connectivity issues in Linux for devices using the popular Broadcom chipset were a common problem that often turned into a difficult, confusing and time-consuming task. Considerable time and effort was often spent performing multiple trial-and-error driver installations, command-line troubleshooting, reading and evaluating technical documentation, and following suggestions from other users to get wireless working.
Although some Linux distros support Broadcom wireless out-of-the-box or provide options within the OS to install the correct drivers/firmware, most do not because of a variety of ongoing development, proprietary and support issues. When users search the Web for answers, this often results in page after page of possible solutions and troubleshooting suggestions, many which may be out-of-date and therefore may no longer work. The amount of information can overwhelm and confuse users desperate for an easy and quick solution. An informative Archlinux.org Wiki entry (2013), Broadcom Wireless, describes many of these issues and illustrates why so much confusion and seemingly conflicting information exists about getting wireless to work for Broadcom devices in Linux.
Current Support Issues
Fortunately, driver/firmware support and installation options for Broadcom wireless devices have steadily improved and don’t require as much user effort or technical expertise as before; however, this doesn’t mean that problems are now a thing of the past. Many users may still need another PC to hunt the Web for the correct drivers, may find themselves the frustrating catch-22 position of needing a LAN connection in order to install the drivers, or learn that the correct drivers are not clearly specified, or when specified, are not included with the installation media.
For some Linux distros, B43 driver/firmware installation can be an automated or a semi-automated process. Some distros feature automatic installation for B43 devices by detecting and installing the appropriate driver package during the OS install from the installation media or through a LAN connection, and some may include them with the kernel image. Others, like Ubuntu/Debian and their derivatives, may even provide customized installation files (like a deb file) from their support forums or web site that can be downloaded and double-clicked to automatically install the appropriate drivers/firmware. Note that some deb files don’t include the drivers and may require a LAN connection in order to download them separately (another catch-22 situation if you don’t have a LAN connection).
When any of the previously mentioned B43 wireless driver/firmware installation options are not available or easily identified, users can still enable wireless using an extraction tool and the open source or proprietary drivers to manually install the firmware – this is the process described in this guide.
Generally, three categories of wireless driver/firmware solutions exist for Linux users with Broadcom chip-sets:
1. brcmsmac/brcmfmac/brcm80211 – Open source kernel driver (newest, often included with the latest kernel images)
2. B43/B43 legacy – Open source reversed-engineered kernel driver (B43 only is covered in this guide, B43 Legacy is not covered)
3. broadcom-wl – Proprietary Broadcom STA driver
The necessary driver/firmware is dependent on the chipset/PCI-ID, type of wireless device, operating system, CPU architecture, and the OS version (note that some Broadcom wireless devices are still unsupported in Linux). Regardless of the chipset/PCI-ID, the distro’s documentation and user forums should always be checked for the latest information since driver solutions and installation options vary from distro to distro and even between versions within a distro.
Identifying the Wireless Device
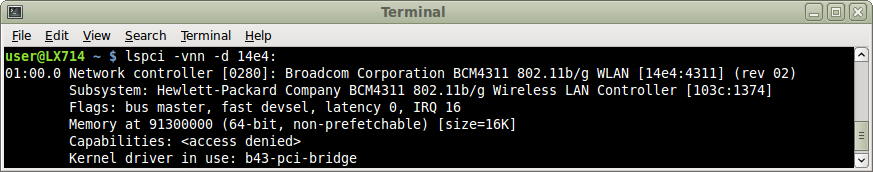
To identify a Broadcom wireless device in Linux, type the following command (case-sensitive) into a terminal:
lspci -vnn -d 14e4:
The above is the output of the lspci command. The PCI-ID is identified within the brackets on the 2nd line by 14e4:4311, where 14e4 is the identification code for Broadcom, and 4311 is the device. In this case, 4311 also identifies the Chip ID. The <access denied> after Capabilities is displayed because the lspci command was executed without using administrator privileges (sudo or su).
Additional wireless identification and troubleshooting commands can be found at the Ubuntu Community Help Wiki.
Tested Solution – Install firmware from driver source file
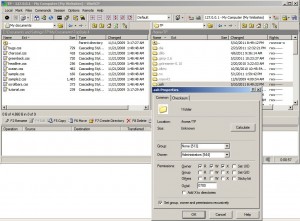
The verified solution for this guide was to use another PC to download the necessary files onto a USB flash drive and then transfer those files to the user directory on the Linux Mint 16 PC with no Internet connectivity. The files needed were fwcutter (a deb file) and the Broadcom-wl proprietary driver source file. Fwcutter is a tool written for BCM43xx driver files to extract firmware from driver source files.
Steps:
1. Download b43-fwcutter for your architecture (bottom of page) from https://packages.debian.org/squeeze/b43-fwcutter. In this case, b43-fwcutter_013-2_amd64.deb was used, but an older version or a 32-bit version probably would have worked as well.
2. Download the source file from https://mirror2.openwrt.org/sources/. In this case, broadcom-wl-4.150.10.5.tar.bz2 was used. Scroll down the page to locate the broadcom files entries.
3. Transfer the files to your user directory on the Linux Mint PC and double-click the b43-fwcutter file to install it. Ignore any warnings about the version being out-of-date.
4. Run the following commands to extract and write the firmware to /lib/firmware. Ignore any warnings.
tar xfvj broadcom-wl-4.150.10.5.tar.bz2 sudo b43-fwcutter -w /lib/firmware broadcom-wl-4.150.10.5/driver/wl_apsta_mimo.o
5. Reboot the PC.
6. The wireless should now work. If so, look for and install any updated B43 wireless firmware/fwcutter/drivers using the Synaptic Package Manager. Do not use B43 legacy.
Other Possible Solutions
Broadcom driver is actually on the installation media. How to install:
https://www.ghacks.net/2015/03/27/how-to-get-wifi-working-in-linux-mint-after-installation/
Ubuntu community wiki. Solutions for a number of PCI-IDs (not tested):
https://help.ubuntu.com/community/BroadcomSTA%28Wireless%29
Deb files. Automatically installs driver/firmware for deb-compatible distros from pkgs.org. Double-click to install (not tested):
https://pkgs.org/download/firmware-b43-installer
References:
B43 wireless information page:
https://wireless.kernel.org/en/users/Drivers/b43
B43 Driver download:
https://mirror2.openwrt.org/sources/
Linux Mint solution:
https://forums.linuxmint.com/viewtopic.php?f=53&t=127202
Ubuntu Community Help Wiki:
https://help.ubuntu.com/community/WifiDocs/WirelessTroubleShootingGuide/Drivers
https://help.ubuntu.com/community/WifiDocs/WirelessTroubleShootingGuide/Commands#lshw